Having purchased the Ubiquiti EdgeRouter ERPOE-5 router awhile back, I have upgraded my home network’s capabilities as a whole.
In addition to a Web Admin UI to configure the router, there is a console port for a physical access to the router and a SSH management access via the ethernet interfaces.
In an effort to secure my router, I elected to use a 15 character password to login to the router. However, being the lazy me, I want to avoid entering the full 15 character password whenever I want to access the router.
On the Web Admin UI side, it is quite simple, as I can simply just use a password manager to manage and remember the password.
On the SSH management console though, I’ll have to copy the password from the password manager whenever I want to access through that route, which can be quite troublesome
This is where passwordless SSH comes in.
Generate the authentication key pair, using ssh-keygen on *nix or PuTTY Key Generator on Windows, and store the private key in a secure location. The public key is what will be used to store on the router.
Normally for a *nix machine, the public key usually goes into the .ssh/authorized_keys file in the user’s home directory.
On the EdgeOS though, the top of the file contains some warning about losing changes
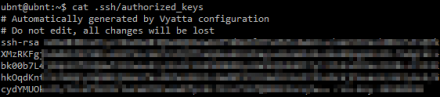
It seems like the setting will not persist across reboots and sure enough, after the next EdgeOS software update and reboot (I love the uptime of the router!), the key was gone from the file!
A bit of googling brought me to this post in the Ubiquiti Forum: ssh authorized_keys
Now the solution only showed the use of the loadkey command, which requires uploading the public key file to the router.
Another way to do it is to use the commandline in configure mode
ubnt@ubnt:~$ configure ubnt@ubnt# set system login user ubnt authentication public-keys <key-name> type ssh-rsa ubnt@ubnt# set system login user ubnt authentication public-keys <key-name> key <base64 encoded public key> ubnt@ubnt# commit ubnt@ubnt# save <key-name>: Arbitrary name for the key <base64 encoded public key>: The base64 public key from PuTTY Key Generator or id_rsa.pub
Viola, now the public key will persist across reboots and will also be exported out when you backup the config.